Proof that my experts were shills & my attorney was apart of the conspiracy alleged on this site.
JanuaryEmailCategory: Litigation
bookmark_borderSo Corrupt Pt.2
I’m at a loss for words. I’m trying to get someone to explain the Eighth Circuit’s decision in my case.
I foolishly thought that the Eighth Circuit would understand that the new report proved – beyond a reasonable doubt – that the government had fabricated and falsified the computer logs that were the sole basis for their case against me and grant the petition.
I, of course, think they’re just biased and believed the AUSA’s nonsense over my arguments but perhaps I’m missing something… The only thing that I think could have made the petition undeniable would be admissions from the shills, so I documented their refusal to answer any questions about their involvement in the conspiracy in Appendix E of the petition. (In my opinion, their documented refusal provides strong circumstantial evidence of their involvement in the conspiracy) Anyway, here’s the report for your review against the government’s evidence.
Expert-Reportbookmark_borderSo Corrupt
I cannot say that I have faith in the Justice System. They, judges, seem to just rubber stamp whatever the authorities say without skepticism. And the lawyers that are supposed to be on your side, just “go through the motions” of “protecting” your constitutional rights, without looking at the case with any skepticism either.
As I’ve documented on this site, I’ve proven that I was railroaded and that the evidence against me was both fraudulent and inadequate. Gotta keep on, keeping on I guess. I’m now fighting in 4 court systems, 8th Circuit (Habeas Case No. 22-2050), 2cd Circuit (appeal), Western District NY Federal Court (motion) & NY State Court (SOR).
The latter is the most frustrating as their whole case was based on the absolute perjury that was contained in my “Pre-Sentencing Report” – even though the federal courts (all of them) disregarded it. This is literally insane!
No-one (judges & government authorities) seems to understand that I was convicted and sentenced for viewing contraband on November 18, 2012 for about 10 minutes (Nebraska Count 2). The government has never proffered what evidence actually supports the WDNY Count 1 conviction with any specificity. Notably, NE court sentenced me on the WDNY count identically (and concurrently) with NE Count 2 without any explanation…
bookmark_borderRailRoaded Part 2
First, To really understand my railroading you must read the 8th Circuit appeal decision regarding US vs. Defoggi (Case No. 15-1209).
The 8th Circuit – without comment – documents the lengths to which the government went to uncover, arrest and then convict a very bad man named Timothy DeFoggi and it reads like a spy novel.
In sum, Tim had several aliases he used to communicate with various individuals about legal and illegal topics. Tim had many legal contacts because he was the “acting” director of cyber security for the US Department of Health and Human Services. Tim also had many illegal contacts regarding his sexual interest in young boys. According to court documents in the Aaron McGrath case – On November 15, 2012 the FBI seized 3 servers (owned by McGrath) that they mysteriously found after allegedly getting a tip from a foreign government. These 3 servers hosted 3 illegal websites named PedoBook, PedoBoard & TB2 in Nebraska.
After seizing his servers the FBI ran them for about 3 weeks to try to determine their users. To this end, the FBI used a “Network Investigation Technique” (NIT) and obtained an invalid warrant in “good faith” to deploy it. (See playpen litigation if interested in the illegality of the NIT Warrant. This topic is more complicated than the playpen litigation because the DeFoggi operation was the NIT’s first use; BUT, none of the attorneys involved asked the question: “Can a Magistrate in Nebraska issue a warrant for NE and elsewhere?” In 2012 that answer was “NO.”, so none of the attorneys asking this question suggests conspiracy.)
Anyway, according to the 8th Circuit, Tim registered on McGrath’s Pedobook on March 2, 2012 with the username “fuckchrist” and the display name “ptasseater”. (Note those two highly identifiable names as you read on.) And this is where things get interesting. First, according to the 8th Circuit’s account, the dates don’t match up. They say he created his Pedobook account on March 2, 2012 but they recite that the FBI’s warrant affidavit states he created the account on or about April 18, 2012. They then say the FBI used Pedobook’s logs to document all the illegal activity conducted by “fuckchrist” on Pedobook. Next, they recite how the FBI connected Timothy to that username and it is, IMO, not technically credible.
Again, in sum, the NIT – allegedly installed on Pedobook – did not work against Tim. So there was no “direct” link from Tim to that site. The court accepted the dubious contention that the FBI connected Tim to these aliases without skepticism. I’m skeptical because the FBI’s claims are technically incredible. They claim that another person under investigation had provided them with information about a person who went by the name of “Jeff” on a site called boylover.net AND that this “Jeff” person used a variety of e-mail addresses including “ptasseater@hotmail.com”. The FBI then used the IP address associated with that hotmail account to get a wiretap on it. The court then recites that the FBI’s informant also provided them with a cell phone number for “Jeff” and told them he had personally met him. The informant then went “undercover” for the FBI and met with Jeff in person. During that meeting – under FBI surveillance – Jeff admitted that his real name was Tim, and that he worked in DC, and that he had a security clearance, and had a boyfriend. The FBI claims to have also had an undercover employee working on Pedobook who was talking with “fuckchrist” and he told him the times he’d be “online” and that his tor-mail account was fuckchrist@tormail.org.
So let’s break this down. According to court documents, on October 26, 2012 the FBI obtains a warrant to deploy malware against Aaron McGrath after a foreign country locates the actual IPs of the three TOR servers in Nebraska and tells the FBI. Again, according to court documents, this malware was serendipitously installed by undisclosed means. As a result of this operation, Aaron McGrath’s servers were seized on November, 15, 2012. The FBI then obtained “void ab intio” warrants in “good faith” to install malware on his three servers to identify their users. This operation was called “Operation Torpedo” and netted the government 15 suspects. However, as mentioned above, their malware – called the NIT – didn’t work against Defoggi’s computer, yet somehow he was arrested on April 9, 2013 with all the other suspects.
I described how my arrest went down in a previous post. Defoggi’s was quite different. According to the 8th Circuit, Tim’s arrest went down like this: they used a wiretap and waited for his IP to be on TOR (that’s all the wiretap could provide because of TOR’s encryption) at the time that “Jeff” told the FBI informant that he’d be online. They then burst into his house and forcibly pulled his laptop from his hands. Upon examination, it contained evidence linking him to those unfortunate aliases and other incriminating evidence.
Now, with all that background, we can discuss how this relates to my railroading. It is my position that the FBI breaks the law to enforce the law, which should be illegal but thanks to various SCOTUS decisions, is mostly legal. (See “pretextual” traffic stops) And when you break the law to enforce the law, – aka the end justifies the means law enforcement – you lose all credibility and morality. (For the most glaring example of this, see the Baltimore Police Department) And that’s how people get railroaded. Many people believe that our government is corrupt, but somehow those same people think that the DOJ is somehow exempt from that corruption, obviously they’re wrong.
The first sign of government corruption, is the refusal to answer questions. This has happened in my case numerous times. Several times in 2014 & 2015, I asked my attorneys “Can a Magistrate in Nebraska issue a warrant to search a computer in NY?” They all ignored the question. When I asked them after the 2016 Playpen rulings – that decided that the answer to my question was NO! – none of them replied. I asked my 3 shill experts [these] 6 questions and they all refused to answer; one said it wasn’t her fault, another said “don’t contact me again” and the other ignored me. I asked one lawyer, Mr. Howard, why he didn’t fire the shills and hire Dr. Mercuri – no reply. I asked another why he challenged the NIT – in a case he handled after mine – on the Magistrate issue and he said he wouldn’t answer my questions unless/until a court ordered him to do so.
The second sign of corruption is lying to avoid defeat. As explained in previous posts, my case was over in November of 2014 when I challenged the NIT based on two anomalies I found in the NIT report used to indict me. On page 2 of the report it shows two session ids that are different when they should be the same. It also shows that the referring page is the same as the current page. Both anomalies indicated fraud. Mr. Becker should have dropped all charges against me at this point, but because he’s corrupt he chose to lie when attempting to explain these two anomalies. When called on his lies, he doubled down instead of folding.
This kind of corruption is the most heinous in my opinion, not just because of what it’s done to me, but because it’s a flagrant abuse of power. If respected government agents lie to a court during a Criminal proceeding, it’s Kafkaesque. How do you fight government lies? Especially when the experts supposed to be on your side are lying in concert with the government. I understand that the technology at the center of this case is complex to “lay people” BUT it’s NOT complex for computer experts as skilled or higher skilled than I. And the things that both parties lied about in my case are so obviously lies, I cannot fathom how my case is still valid. (Something the 8th Circuit should rectify soon). The lies are so obvious to tech people that I can only explain them by conspiracy.
The first lie is absurd on its face – well technically absurd -; they claimed that “the NIT was a flash application”. Simple logic proves this incorrect, as at a minimum, three parts would be required for the NIT to identify the actual IP address of a TOR user. This lie was needed to further the government’s false narrative and hide the fact that, in the case of TB2, the government lied to the grand jury about the admissibility and veracity of the NIT evidence. In other words, the NIT, in the case of TB2 didn’t provide any evidence of a crime and any testimony claiming that it did was perjury.
The next lie was more subtile. The government claimed that TB2 issued session ids to clients & tracked visitor activity in logs. Both claims were blatant lies BUT they were supported by my experts. Because of their misconduct I now refer to them as government shills (“shills”). As the “new” expert report now before the 8th Circuit proves; TB2’s software (Tinyboard) doesn’t issue session ids to clients or track their activity in any way.
The third lie was their most credible upon first glance but falls apart upon close inspection. They claimed to have found “suspected” images on two devices out of the seventeen they stole from me on April 9, 2013. First problem with this claim is that both devices are the operating system drives for the computers in question. The next problem is that MOST of the SUSPECTED images are in locations inaccessible to humans without special software. In other words, you cannot see them without forensic software AND the ability to carve them out of unallocated space. The remaining images were discussed in a previous post, i.e. planted by the FBI forensic tech while at my house on April 9, 2013. (Note these additional “images” are ALL thumbnails in a hidden directory created by the linux operating system in Adama’s somehow unencrypted home directory. According to the FBI ALL the thumbnails have meta data that indicate the images they represent were are on a truecrypt volume that the FBI did not find.) Therefore the suspected images are not credible, considering the FBI didn’t describe a single image. The only government agent to describe an image regarded my stolen PS3, which had a picture of Yoona on it. They described her as an asian female of 16 or 17 years old. That, of course was perjury. Yoona in the picture in question was 23 years old. That claim alone proves they have no idea what they’re talking about when it comes to the actual ages of women in images.
bookmark_borderExoneration Frustrations
What’s frustrating is how many lies were told and how hard it is to address them as a convict. When you accuse the government of fabricating, falsifying and planting evidence, in this case planting hidden files in an encrypted directory that is now somehow unencrypted, everyone rolls their eyes… even though it’s the only explanation.
Fraudulent Indictment
On March 20, 2013, the government obtained a John Doe indictment against Kirk Cottom for visiting a site named TB2 on the TOR network. My petition soon to be before the Eighth Circuit, proves – beyond a reasonable doubt – that the indictment was procured with perjury about fabricated and falsified computer logs.
Planting Evidence
On April 9, 2013, when the FBI showed up at my house, they violated the knock and announce rule. That rule states that they must knock on your door and wait for an answer. When the “target” opens the door they must announce why they’re at your house. In this case, the FBI was required to announce they were at my house to execute a search warrant. Instead, in clear violation of this rule, they knocked and talked. This is the constitutional rule that when the FBI doesn’t have a search warrant they can knock on your door and try to talk you into allowing them to search. So I assumed they were on a knock and talk fishing expedition and talked to them; BUT, when they asked for permission to search, I asked them to leave.
That’s when they revealed that they had a search warrant. I told them they were required to tell me that at my door. They shrugged and told me to take it up with the judge. They then searched my linux computer’s 500GB Operating system drive. After about an hour of finding nothing, they opened my Windows Laptop and found my picture associated with an account named Adama on the Lock Screen. I thought “if these clowns come back in a few minutes claiming to have found something in the Adama account on the linux box I’ll know the fix is in…”
Sure enough, a few minutes later they claim to have found images in Adama’s home directory. I exclaim “bullshit!” For two reasons: 1) The Adama account on the linux box was NEVER used. AND 2) The home directories for all three accounts Kirk, Simon and Adama were encrypted, so it would be impossible to find any files in any of the home directories.
About a year later, I get the forensic report from the FBI and it states that Kirk & Simon are encrypted BUT Adama isn’t. The FBI tech notes that the Adama account is locked by the operating system. I tell my lawyer this is because the FBI over-wrote Adama’s encrypted home directory, when the FBI tech booted the image of the tampered with linux system, it noticed the now unencrypted Adama account and locked it. My lawyer ignored me and no-one besides the FBI tech ever examined the drive.
bookmark_borderThat’s Suspicious
So on March 27, 2022 I sent a message to the lead shill in my case, Dr. Podhradsky. I asked her these six questions:
- When and how did attorney Joseph Gross Jr. involve you with my case?
- Why did you examine the wrong server for your first report in January of 2015?
- Why did you parrot the government’s lie that the NIT was just a flash application?
- When and how did attorney Joseph Howard involve you with my case?
- Why did you lie about Tinyboard software in your June [2015] report?
- Did you communicate about this case with Keith A Becker?
Last week I received her reply. It said words to the effect of “It’s not my fault, contact Dr. Miller” and she gave me his possible contact info. I e-mailed the info@company.com address to see if they could put me in contact with Dr. Miller. Much to my surprise, I got a reply that same day from his company e-mail account. I sent him a pdf of the letter I sent Dr. Podhradsky with some elaboration in the e-mail. He responded:
If you have time, you could give me a phone call and maybe I can clear up some of the points in here that may be confusing.
Dr. Matt Miller
I responded that I didn’t think a phone conversation would be productive and would he please answer my 6 questions. (and perhaps two more). He responded:
Dear Kirk Cottom,
Dr. Matt Miller
Post conviction appellate concerns are typically handled by counsel and I will refer you to counsel who saw you this far in the process. I have included Joe Howard on this email so he is aware of your attempt to contact me, and I appreciate that you will not contact me again, unless through counsel. Any further and continued efforts will be met by legal action. Thank you.
Maybe it’s just me, but I find this response suspicious…
bookmark_borderExoneration takes a long time
If I’ve learned anything from researching those falsely accused is that it takes a very long time to get the courts to vacate unjustified convictions. So I just have to accept that and keep on keeping on.
bookmark_borderFalse Narrative
This Table:
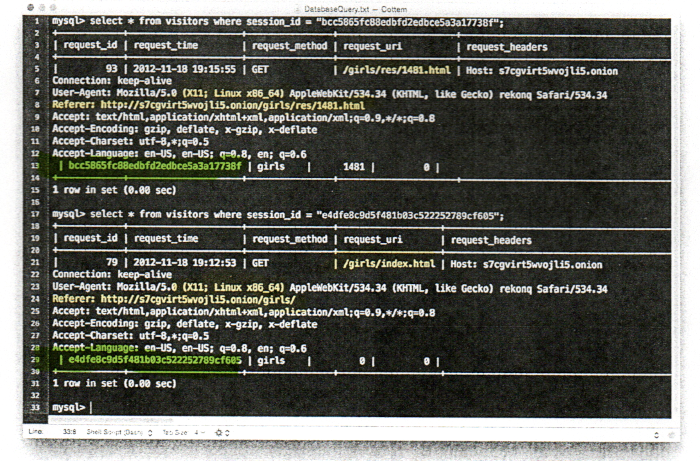
Does Not Support the Government’s Narrative:
On November 18, 2012, a user with IP address 69.207.147.71 accessed “Website A” and was presented with different sections to choose from and access further, including, but not limited to the following: “pre-teen boys”, “teen-aged boys”, “teen-aged girls”, “babies/toddlers”, and “fetishes”. The user with IP address 69.207.147.71 selected the section “PT girls”. After selecting the “PT girls” section, the user with IP address 69.207.147.71 was presented with the webpage with the title “/girls/pt girls” at the top of the page. Several board image threads were displayed on that page including thumbnail images from various threads. One of the threads, thread “1481”, had the subject title “finger bum girl” and displayed three thumbnail images from that particular thread. The images displayed included images with the file names dsc03248, dsc03286 and dsc03287. The images ending in 286 and 287 are close up pictures of a prepubescent vagina being digitally penetrated. The thread could be accessed by either clicking on the link to the thread with the subject “finger bum girl” or by clicking on one of the three images displayed. The user with IP address 69.207.147.71 then selected the 1481 thread with the identified subject, “finger bum girl”, and accessed a webpage that contained all the images available on that thread, consisting of over thirty pictures of a young girl, with many of them containing images depicting sexually explicit conduct. All the pictures would have appeared once the user clicked the 1481 thread with the identified subject, “finger bum girl”, or clicked on one of the three displayed thumbnail images.
Therefore, the conviction is invalid and is why I’m still litigating the matter today.
bookmark_borderI was railroaded
I (Kirk Cottom) was Railroaded
The meaning of being railroaded according to my computer’s dictionary is to “press (someone) into doing something by rushing or coercing them.”
The timeline of the railroading is such:
July 28, 2015: I fly out to Nebraska to see Mr. Becker’s “evidence book”.
July 29, 2015: I view the evidence book with my Attorney, Mr. Howard and his “expert”, Mr. Kasel. I’m not impressed and order Mr. Howard to prepare for the Daubert hearing and trial. (If I won the Daubert hearing the case was over, if I lost the hearing we would proceed to trial, both scheduled for August 3, 2015.) I fly back to Rochester that evening and return to work the next day.
July 30, 2015 (8am to 4pm): Mr. Howard e-mails me all day, trying to get me to agree to allow him to negotiate a plea I’d enter into if we lost the Daubert hearing on August 3, 2015. I repeatedly order Mr. Howard to prepare for trial and that he did not have permission to negotiate any plea deal. He then tries to call me on the phone, I refuse to answer.
July 30, 2015 (4pm to 6pm): A little after 4pm, Mr. Slawinski e-mails me and asks if I would come to his office, I agree. Once there I’m ambushed by him, Mr. Howard and Mr. Gross to accept a “conditional plea” deal, that none of them had permission to negotiate. They coerce me into agreeing to the conditional plea by convincing me that it was like a “Nolo contendere” plea, when they knew that it wasn’t.
August 1, 2015: I fly back to Nebraska and inform Mr. Howard I don’t like the plea deal. He says lets focus on winning the Daubert motion.
August 3, 2015: I lose the flawed Daubert hearing. It was flawed because both the government and the defense experts perjured themselves on multiple issues. Their lies included:
1) Stating that the FBI’s Network Investigative Technique (NIT) was just the “exploit code”. (In my case a flash application.) This lie was debunked in subsequent litigation. (The FBI tried this false narrative again while prosecuting “Operation Pacifier” cases, based on the infamous “playpen” website. All those cases rejected this false narrative and adjudicated that the NIT consisted of 4 parts. That was “prejudicial” because my Daubert hearing was based on a knowingly false narrative.)
2) That perjury, exposed many others. Like lying about the code on TB2’s server. Those lies included: claiming that Tinyboard (the software that ran TB2) had a visitors table, claiming that Tinyboard issued sessionID’s to clients and claiming both the fraudulent items were admissible at trial when they knew they were both inadmissible per FED. R. EVID 803(6) & 803(8). That cause Mr. Becker’s team to present that data as “Expert Summary Evidence” to circumvent its exclusion from trial.
3) All Those perjuries helped hide the biggest perjury of this case, the fact that the NIT report (and it’s underlying documents, Dr. Edman’s computer logs, populated by his scripts) do not provide any evidence for a crime, because none of it has any information about images. This means that the Nebraska indictment was fraudulently obtained and thus invalid.
Since all the above is irrefutable, it is absolute proof that I was railroaded.
bookmark_borderMalicious Prosecution
November 17, 2012: Keith Becker’s team fraudulently obtains a “void ab initio” Network Investigation Technique (NIT) warrant. It was fraudulent because the data they said they were obtaining was going to be fabricated and falsified; and, even if it wasn’t, all the data would be inadmissible at trial per Federal Rules of Evidence 803(6) & 803(8). (Rule 803(6) prohibits documents that are created for the sole purpose of litigation and rule 803(8) prohibits police reports.)
The warrant was void ab initio because the Magistrate in Nebraska had no authority to issue a warrant to search a computer in New York.
November 18, 2012: my linux computer sends a “computer under FBI control” two encrypted messages. One at 7:13pm CST and then another at 7:16pm CST. Each message was 98 characters and contained similar information. Both messages labeled board_id as “2” and method as “swf”. The only difference between the two messages was what they called a “session”. The session for the 7:13pm message was e4dfe8c9d5f481b03c522252789cf605 and for the 7:16pm message is was bcc5865fc88edbfd2edbce5a3a17737f.
January 18, 2013: Mr. Becker’s team generates a “TB2” NIT report. It consists of 3 pages. The source of the information on the first page was Time Warner, it indicated that the IP in question was assigned to my house at the time of the alleged crime. The source of the information on the second page was Dr. Edman’s fabricated “visitors” table that he populated with falsified information with a script he called gallery.php. The source of the information on the third page was also provided by a fabricated table and populated with a script (cornhusker.py) that Dr. Edman coded solely for criminal prosecution.
The federal rules of evidence mentioned above clearly prohibit the use of Dr. Edman’s tables at trial. Since the Becker team knew this, they presented this data in their NIT Report as “Expert Summary Evidence” and failed to disclose the source of the information on pages 2 and 3 of their report, on purpose, to evade those federal rules of evidence. This conduct established bad faith.
March 20, 2013: Mr. Becker’s team fraudulently obtains an indictment from a grand jury in Nebraska based solely on the NIT Report that they generated on January 18, 2013.
That created many problems for Mr. Becker’s team:
1) As mentioned above, the federal rules of evidence clearly preclude this evidence from trial. That makes any indictment obtained solely with that NIT report potentially frivolous. (If the government obtains an indictment with evidence that is inadmissible at trial, it must believe that it will probably find admissible evidence before trial.)
2) Mr. Becker’s team has testified that page 2 of their NIT report (Dr. Edman’s fabricated and falsified “visitors” table) is evidence of a crime. Specifically, they testified that it was proof that a web browser running on my linux computer viewed illegal images on a website called TB2, because it loaded two html files, one called “index.html” at 7:12pm CST and then another named “1481.html” at 7:15pm CST. Unfortunately, this is a claim that is easily debunked. As Gerry Grant testified at US v. Raymonda’s suppression hearing in 2013, when you view a webpage, your browser makes a series of “GET REQUESTS”. First, it requests the html file. After it receives it, it then requests the other items to finish the page, among these other requests are “image” requests. Most browsers are configured to automatically make these requests for images, BUT you can configure the browser NOT to make them. You can also configure the browser to ignore java, javascript and flash application requests.
The only way to know if a given IP requested a given file is to view the web server’s logs. In the case of TB2’s server, those logs would be useless as the only IP in its logs would be the last node the traffic went through. (TB2 was being hosting on a type of VPN called the Onion Router or TOR). Therefore any testimony given before the grand jury in Nebraska that the FBI’s NIT report provided evidence of a crime was perjury as it only contained evidence that index.html and 1481.html were requested. Dr. Edman’s visitors table doesn’t provide ANY evidence that ANY images were requested, thus it doesn’t provide any evidence that a crime was committed. In other words, viewing those HTML files would never be a crime, because they are just text files.
3) The only thing that ties that non-criminal activity (requesting index.html and 1481.html) to my IP address is Dr. Edman’s cornhusker.py log that’s presented on the NIT Report’s third page. As mentioned above, this page would be inadmissible at trial because it was created by law enforcement, solely for prosecution. As mentioned above, this log suggests that the FBI’s flash application was running on my linux computer at 7:13pm CST and 7:16pm CST and that flash app sent those two encrypted messages after being requested by my browser after loading those two html files at 7:12pm CST and 7:15pm CST.
As you can see the FBi’s narrative has five major flaws:
1) As explained above, page 2 doesn’t provide any probable cause to believe a crime has been committed.
2) Page 2 is based on a fabricated table (TB2 runs of PHP software called Tinyboard, Tinyboard doesn’t have a visitors table).
3) That fabricated table contains falsified evidence (Tinyboard doesn’t generate sessionIDs for visitors). The request_uri is also falsified. This forgery makes it impossible to determine the actual proceeding page. It means they cannot testify, in good faith, about a visit progression because their visitors table reports that the request_uri is the same page as the referring page. (For example: normally when you click a link for page B on page A the request_uri will be page B and the referring page will be page A. The forgeries generated by Dr. Edman’s scripts on TB2 always show the request_uri as page B and the referring page as page B)
4) Dr. Edman’s fabricated tables, and the falsified information he puts in them, are a form of perjury.
5) There is a strong possibility that none of this information was generated by human action. That is because the flash application takes too long to execute. The logs state that the flash application for “session” e4dfe8c9d5f481b03c522252789cf605 took 39 seconds to execute and for “session” bcc5865fc88edbfd2edbce5a3a17737f it took 63 seconds. Now, in human time that isn’t too long, but in the world of computers that’s a ridiculously long amount of time. Here are the sequence of events:
- At 7:12pm my browser requested index.html. According Dr. Edman’s table, his script, gallery.php was loaded at 7:12:53 in a hidden iframe.
- gallery.php then presented the browser with javascript to load Dr. Edman’s gallery.swf that the browser would execute it immediately.
- once the flash app was loaded it would make a dns query for the IP of the server that was running Dr. Edman’s cornhusker.py (a server that the FBI destroyed)
- the dns request was ridiculously long. It was 96.126.124.96.(98 character encrypted text).cpimagegallery.com and it negated the need to establish a socket connection to cornhusker.py, because the dns request reveals the true IP and the falsified sessionID.
- Regardless, cornhusker.py should have responded to the requests in milliseconds and then the flash app would request permission to communicate milliseconds later. Therefore the whole transaction should have taken less than 3 seconds. However, the first transaction took 39 seconds and the second took an astonishing 63 seconds. In the world of DNS, every request after the first should be much faster than the first. The fact that it took significantly longer strongly suggests shenanigans were afoot.
- We’ll never be able to determine what happened because the FBI destroyed the server (along with its logs) that could shed light on this egregious anomaly.
It’s abundantly clear that Mr. Becker’s team presented the Nebraska grand jury with false information and that information was the sole basis for the indictment. That means that the indictment was obtained fraudulently. Therefore the whole prosecution was malicious and must be vacated.