First, To really understand my railroading you must read the 8th Circuit appeal decision regarding US vs. Defoggi (Case No. 15-1209).
The 8th Circuit – without comment – documents the lengths to which the government went to uncover, arrest and then convict a very bad man named Timothy DeFoggi and it reads like a spy novel.
In sum, Tim had several aliases he used to communicate with various individuals about legal and illegal topics. Tim had many legal contacts because he was the “acting” director of cyber security for the US Department of Health and Human Services. Tim also had many illegal contacts regarding his sexual interest in young boys. According to court documents in the Aaron McGrath case – On November 15, 2012 the FBI seized 3 servers (owned by McGrath) that they mysteriously found after allegedly getting a tip from a foreign government. These 3 servers hosted 3 illegal websites named PedoBook, PedoBoard & TB2 in Nebraska.
After seizing his servers the FBI ran them for about 3 weeks to try to determine their users. To this end, the FBI used a “Network Investigation Technique” (NIT) and obtained an invalid warrant in “good faith” to deploy it. (See playpen litigation if interested in the illegality of the NIT Warrant. This topic is more complicated than the playpen litigation because the DeFoggi operation was the NIT’s first use; BUT, none of the attorneys involved asked the question: “Can a Magistrate in Nebraska issue a warrant for NE and elsewhere?” In 2012 that answer was “NO.”, so none of the attorneys asking this question suggests conspiracy.)
Anyway, according to the 8th Circuit, Tim registered on McGrath’s Pedobook on March 2, 2012 with the username “fuckchrist” and the display name “ptasseater”. (Note those two highly identifiable names as you read on.) And this is where things get interesting. First, according to the 8th Circuit’s account, the dates don’t match up. They say he created his Pedobook account on March 2, 2012 but they recite that the FBI’s warrant affidavit states he created the account on or about April 18, 2012. They then say the FBI used Pedobook’s logs to document all the illegal activity conducted by “fuckchrist” on Pedobook. Next, they recite how the FBI connected Timothy to that username and it is, IMO, not technically credible.
Again, in sum, the NIT – allegedly installed on Pedobook – did not work against Tim. So there was no “direct” link from Tim to that site. The court accepted the dubious contention that the FBI connected Tim to these aliases without skepticism. I’m skeptical because the FBI’s claims are technically incredible. They claim that another person under investigation had provided them with information about a person who went by the name of “Jeff” on a site called boylover.net AND that this “Jeff” person used a variety of e-mail addresses including “ptasseater@hotmail.com”. The FBI then used the IP address associated with that hotmail account to get a wiretap on it. The court then recites that the FBI’s informant also provided them with a cell phone number for “Jeff” and told them he had personally met him. The informant then went “undercover” for the FBI and met with Jeff in person. During that meeting – under FBI surveillance – Jeff admitted that his real name was Tim, and that he worked in DC, and that he had a security clearance, and had a boyfriend. The FBI claims to have also had an undercover employee working on Pedobook who was talking with “fuckchrist” and he told him the times he’d be “online” and that his tor-mail account was fuckchrist@tormail.org.
So let’s break this down. According to court documents, on October 26, 2012 the FBI obtains a warrant to deploy malware against Aaron McGrath after a foreign country locates the actual IPs of the three TOR servers in Nebraska and tells the FBI. Again, according to court documents, this malware was serendipitously installed by undisclosed means. As a result of this operation, Aaron McGrath’s servers were seized on November, 15, 2012. The FBI then obtained “void ab intio” warrants in “good faith” to install malware on his three servers to identify their users. This operation was called “Operation Torpedo” and netted the government 15 suspects. However, as mentioned above, their malware – called the NIT – didn’t work against Defoggi’s computer, yet somehow he was arrested on April 9, 2013 with all the other suspects.
I described how my arrest went down in a previous post. Defoggi’s was quite different. According to the 8th Circuit, Tim’s arrest went down like this: they used a wiretap and waited for his IP to be on TOR (that’s all the wiretap could provide because of TOR’s encryption) at the time that “Jeff” told the FBI informant that he’d be online. They then burst into his house and forcibly pulled his laptop from his hands. Upon examination, it contained evidence linking him to those unfortunate aliases and other incriminating evidence.
Now, with all that background, we can discuss how this relates to my railroading. It is my position that the FBI breaks the law to enforce the law, which should be illegal but thanks to various SCOTUS decisions, is mostly legal. (See “pretextual” traffic stops) And when you break the law to enforce the law, – aka the end justifies the means law enforcement – you lose all credibility and morality. (For the most glaring example of this, see the Baltimore Police Department) And that’s how people get railroaded. Many people believe that our government is corrupt, but somehow those same people think that the DOJ is somehow exempt from that corruption, obviously they’re wrong.
The first sign of government corruption, is the refusal to answer questions. This has happened in my case numerous times. Several times in 2014 & 2015, I asked my attorneys “Can a Magistrate in Nebraska issue a warrant to search a computer in NY?” They all ignored the question. When I asked them after the 2016 Playpen rulings – that decided that the answer to my question was NO! – none of them replied. I asked my 3 shill experts [these] 6 questions and they all refused to answer; one said it wasn’t her fault, another said “don’t contact me again” and the other ignored me. I asked one lawyer, Mr. Howard, why he didn’t fire the shills and hire Dr. Mercuri – no reply. I asked another why he challenged the NIT – in a case he handled after mine – on the Magistrate issue and he said he wouldn’t answer my questions unless/until a court ordered him to do so.
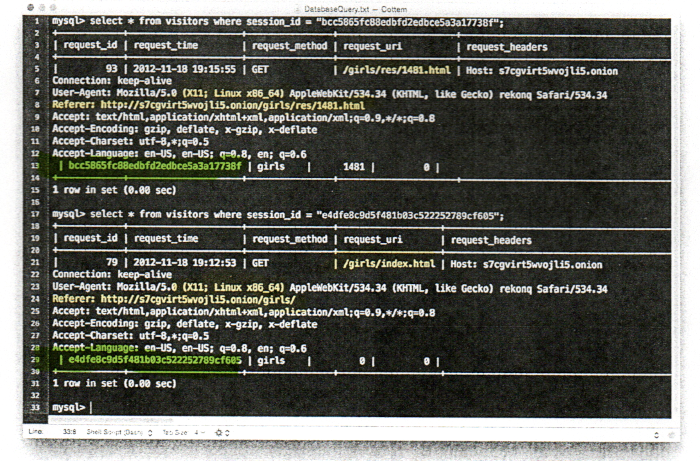
The second sign of corruption is lying to avoid defeat. As explained in previous posts, my case was over in November of 2014 when I challenged the NIT based on two anomalies I found in the NIT report used to indict me. On page 2 of the report it shows two session ids that are different when they should be the same. It also shows that the referring page is the same as the current page. Both anomalies indicated fraud. Mr. Becker should have dropped all charges against me at this point, but because he’s corrupt he chose to lie when attempting to explain these two anomalies. When called on his lies, he doubled down instead of folding.
This kind of corruption is the most heinous in my opinion, not just because of what it’s done to me, but because it’s a flagrant abuse of power. If respected government agents lie to a court during a Criminal proceeding, it’s Kafkaesque. How do you fight government lies? Especially when the experts supposed to be on your side are lying in concert with the government. I understand that the technology at the center of this case is complex to “lay people” BUT it’s NOT complex for computer experts as skilled or higher skilled than I. And the things that both parties lied about in my case are so obviously lies, I cannot fathom how my case is still valid. (Something the 8th Circuit should rectify soon). The lies are so obvious to tech people that I can only explain them by conspiracy.
The first lie is absurd on its face – well technically absurd -; they claimed that “the NIT was a flash application”. Simple logic proves this incorrect, as at a minimum, three parts would be required for the NIT to identify the actual IP address of a TOR user. This lie was needed to further the government’s false narrative and hide the fact that, in the case of TB2, the government lied to the grand jury about the admissibility and veracity of the NIT evidence. In other words, the NIT, in the case of TB2 didn’t provide any evidence of a crime and any testimony claiming that it did was perjury.
The next lie was more subtile. The government claimed that TB2 issued session ids to clients & tracked visitor activity in logs. Both claims were blatant lies BUT they were supported by my experts. Because of their misconduct I now refer to them as government shills (“shills”). As the “new” expert report now before the 8th Circuit proves; TB2’s software (Tinyboard) doesn’t issue session ids to clients or track their activity in any way.
The third lie was their most credible upon first glance but falls apart upon close inspection. They claimed to have found “suspected” images on two devices out of the seventeen they stole from me on April 9, 2013. First problem with this claim is that both devices are the operating system drives for the computers in question. The next problem is that MOST of the SUSPECTED images are in locations inaccessible to humans without special software. In other words, you cannot see them without forensic software AND the ability to carve them out of unallocated space. The remaining images were discussed in a previous post, i.e. planted by the FBI forensic tech while at my house on April 9, 2013. (Note these additional “images” are ALL thumbnails in a hidden directory created by the linux operating system in Adama’s somehow unencrypted home directory. According to the FBI ALL the thumbnails have meta data that indicate the images they represent were are on a truecrypt volume that the FBI did not find.) Therefore the suspected images are not credible, considering the FBI didn’t describe a single image. The only government agent to describe an image regarded my stolen PS3, which had a picture of Yoona on it. They described her as an asian female of 16 or 17 years old. That, of course was perjury. Yoona in the picture in question was 23 years old. That claim alone proves they have no idea what they’re talking about when it comes to the actual ages of women in images.